Healthcare CIOs Prepare For HIPAA Update
Forbes Healthcare
JANUARY 6, 2025
These changes to HIPAA, outlined in a Notice of Proposed Rulemaking (NPRM), aim to increase cybersecurity protections for electronic protected health information (ePHI).
This site uses cookies to improve your experience. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country, we will assume you are from the United States. Select your Cookie Settings or view our Privacy Policy and Terms of Use.
Cookies and similar technologies are used on this website for proper function of the website, for tracking performance analytics and for marketing purposes. We and some of our third-party providers may use cookie data for various purposes. Please review the cookie settings below and choose your preference.
Used for the proper function of the website
Used for monitoring website traffic and interactions
Cookies and similar technologies are used on this website for proper function of the website, for tracking performance analytics and for marketing purposes. We and some of our third-party providers may use cookie data for various purposes. Please review the cookie settings below and choose your preference.
 HIPAA Related Topics
HIPAA Related Topics 
Forbes Healthcare
JANUARY 6, 2025
These changes to HIPAA, outlined in a Notice of Proposed Rulemaking (NPRM), aim to increase cybersecurity protections for electronic protected health information (ePHI).
The HIPAA Journal
MARCH 26, 2025
Department of Health and Human Services (HHS) Office for Civil Rights (OCR) has confirmed that the long-awaited third phase of its HIPAA compliance audits is underway and will involve HIPAA compliance audits of 50 covered entities and business associates. OCRs workload has increased considerably, yet its budget has remained flat.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Electronic Health Reporter
OCTOBER 20, 2020
It is a HIPAA law created to ensure that all of […]. The article Why Are HIPAA Risk Assessments Important? By Chase Higbee, lead IT strategist, Atlantic.Net. A risk assessment is a mandatory annual task completed by a covered entity and a business associate. appeared first on electronichealthreporter.com.

Electronic Health Reporter
MARCH 24, 2021
Anyone dealing with healthcare IT in the US will come across HIPAA and HITECH and HITRUST — and it’s easy to get them confused. The article HIPAA, HITECH and HITRUST In Healthcare IT appeared first on electronichealthreporter.com. Illegal copying is prohibited. By Gerry Miller, CEO, Cloudticity.

Electronic Health Reporter
DECEMBER 7, 2020
The Healthcare Insurance Portability and Accountability Act (HIPAA) was adopted in 1996. The article Crucial Lessons From Past HIPAA Non-Compliance Cases appeared first on electronichealthreporter.com.

Electronic Health Reporter
APRIL 29, 2021
Congress enacted the Health Insurance Portability and Accountability Act (HIPAA) in 1996. The article Expect More From HIPAA Proposed Changes: Easing Information Flow Shouldn’t Mean Reducing Health Data Privacy appeared first on electronichealthreporter.com. By Deborah Hsieh, chief policy and strategy officer, Ciox Health.

The HIPAA Journal
DECEMBER 24, 2022
Penalties for HIPAA violations can be issued by the Department of Health and Human Services’ Office for Civil Rights (OCR) and state attorneys general. In addition to financial penalties, covered entities are required to adopt a corrective action plan to bring policies and procedures up to the standards demanded by HIPAA. .

Electronic Health Reporter
JANUARY 15, 2021
The Health Insurance Portability and Accountability Act (HIPAA) affects thousands of organizations across the […]. The article Challenges of Maintaining HIPAA Compliance: 9 Pain Points appeared first on electronichealthreporter.com. Organizations are facing greater scrutiny in this increasingly regulated world.

The HIPAA Journal
APRIL 27, 2025
HIPAA violation cases are compliance investigations that result from a data breach being notified to the Department of Health and Human Services’ (HHS) Office for Civil Rights (OCR) or a privacy complaint being submitted to OCR via the complaints portal. There are many different types of HIPAA violation cases.

The HIPAA Journal
APRIL 26, 2024
The Society of Corporate Compliance and Ethics (SCCE) has recently accredited ComplianceJunction’s ‘HIPAA Training for Organizations’ training course. The training has been used by more than 1,000 healthcare organizations and over 100 universities to raise awareness of the HIPAA regulations.

Valant
SEPTEMBER 30, 2024
However, with this digital transformation comes the critical need for HIPAA compliant teletherapy platforms. What is HIPAA and Why is it Crucial in Teletherapy? The Health Insurance Portability and Accountability Act (HIPAA) sets the standard for protecting sensitive patient data.
Healthcare Dive - Practice Management
MARCH 14, 2025
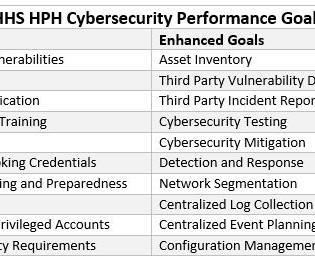
A new proposed rule aims to significantly amend the HIPAA security rule — these are the key updates to know.

The HIPAA Journal
MARCH 21, 2025
A New York woman has avoided a jail term for a criminal violation of the Health Insurance Portability and Accountability Act (HIPAA), having been sentenced to probation. The Federal Bureau of Investigation (FBI) investigated and DAgostino was arrested and charged for the HIPAA violation. in restitution.
Electronic Health Reporter
JUNE 16, 2021
The Health Insurance Portability and Accountability Act of 1996 (HIPAA) is a federal law that mandates the creation of national standards to protect delicate and private patient medical history and health information from being disclosed […]. Illegal copying is prohibited.

The HIPAA Journal
MAY 1, 2025
The plaintiffs claimed that Somnia was negligent by failing to implement appropriate cybersecurity safeguards to ensure the privacy and confidentiality of the data stored on its network, did not follow industry security standards, and was not fully compliant with the HIPAA Rules. The post Somnias $2.4
Physicians Practice
AUGUST 9, 2024
Each practice should learn from the result of this HIPAA case.

The HIPAA Journal
APRIL 29, 2025
The OCR breach portal still lists the incident as affecting 112,726 patients and plan members of its HIPAA-regulated entity clients, although that total may well be updated in the coming days. The post Verisource Services Increases Data Breach Victim Count to 4 Million appeared first on The HIPAA Journal.

Electronic Health Reporter
NOVEMBER 22, 2022
HIPAA-compliant uses of SMS messaging may not be as common as […]. The article HIPAA-Compliant Uses of SMS Messaging appeared first on electronichealthreporter.com. Shannon Flynn is a freelance blogger who covers education technologies, cybersecurity and IoT topics.

99MGMT
MAY 21, 2024
Social media HIPAA violations are surprisingly common. Here are some uncomfortable examples that caused compliance issues for clinics.

Pulmonology Advisor - Practice Management
MAY 17, 2024
An update to the Health Insurance Portability and Accountability Act (HIPAA) Security Rule is now underway with new cybersecurity requirements. An update to the HIPAA Security Rule is planned for this spring and it will include new cybersecurity requirements. A serious concern is the tracking of patient data.

The HIPAA Journal
MARCH 31, 2025
Multiple Hospitals appeared first on The HIPAA Journal. Oracle Cloud maintains that there was no breach of Oracle Cloud and none of the published credentials are for Oracle Cloud, but has not provided any official explanation. The post Oracle Health Breach Affects Patients of Multiple U.S.
The HIPAA Journal
APRIL 17, 2025
One of the objectives of the HIPAA Journal 2024/25 Annual Survey was to obtain insights into HIPAA compliance best practices. If finalized, the proposals will not only become standards required for HIPAA compliance , but may also be adopted by CMS as conditions for participation in Medicare and Medicaid.

Northwest Career College
APRIL 30, 2025
HIPAA is a short form of the Health Insurance Portability and Accountability Act , a law devised to protect patients’ personal information regarding their health conditions. The following article will explain why HIPAA compliance is significant in medical billing and coding and how it helps protect patients and providers.

The HIPAA Journal
APRIL 29, 2025
The post Ascension Notifying Patients About Data Breach at Former Business Partner appeared first on The HIPAA Journal. Carolina Anesthesiology is located in High Point, North Carolina, and provides anesthesiology services to High Point Regional Health System and Atrium Health.

Electronic Health Reporter
MAY 17, 2024
Today, telehealth enables healthcare providers to expand access to medical […] The article A HIPAA-Compliant Path to Efficiency and Relief with Telehealth appeared first on electronichealthreporter.com. We’ve come a long way since the University of Nebraska pioneered two-way video communication for telemedicine in 1959.

The HIPAA Journal
MARCH 26, 2025
The lawsuit also claims the medical group was in violation of the Health Insurance Portability and Accountability Act (HIPAA), drawing attention to 10 alleged violations of the HIPAA Rules.The lawsuit also took issue with the length of time it took for the affected individuals to discover their sensitive data had been compromised.

The HIPAA Journal
APRIL 30, 2025
The implication of this requirement if finalized – is that covered entities will only be permitted to contract services from business associates that can demonstrate compliance with HIPAA. Despite the variety of compliance requirements, some areas of HIPAA compliance are common to all business associates.
Healthcare Dive - Practice Management
JANUARY 3, 2025
The update, which would be the first since 2013, aims to clarify and provide more instruction on securing health data as cyberattacks and breaches in the sector skyrocket.
The HIPAA Journal
APRIL 18, 2025
The post Cybersecurity Firm CEO Charged with Installing Malware on a Hospital Computer appeared first on The HIPAA Journal. Felony convictions see the penalties increased to a fine of up to $100,000 and/or a jail term between 1 and 10 years.

The HIPAA Journal
MARCH 21, 2025
Hospitals About Potential Terror Threat appeared first on The HIPAA Journal. Also, increasing relationships with local and federal law enforcement may streamline response efforts during an attack, explained the AHA and Health-ISAC. The post AHA; Health-ISAC Warn U.S.

The HIPAA Journal
MARCH 18, 2025
An amendment to the law has been signed by state governor Andy Beshear that narrows the scope of the law, exempting information collected by healthcare providers covered under HIPAA that maintain protected health information in compliance with the HIPAA Rules and other related regulations. 8 164.514(e).

The HIPAA Journal
MARCH 28, 2025
The HHS Office for Civil Rights issued guidance for HIPAA-regulated entities on the use of these tools, which OCR said could violate HIPAA. The post Website Tracking Lawsuit Against Orlando Health Survives Motion to Dismiss appeared first on The HIPAA Journal. The lawsuit W.W.

Scrubs
AUGUST 8, 2023
However, with HIPAA and patient privacy concerns, some nurses may be disciplined for this if it isn’t done at appropriate times. Under HIPAA, facilities “must implement device and media controls as a part of their physical safeguards.”
Healthcare Dive - Practice Management
NOVEMBER 26, 2024
The HHS’ Office for Civil Rights’ audit program was too narrow in scope to effectively assess data protections and reduce cyber risks in the healthcare sector, according to the report.

The HIPAA Journal
APRIL 16, 2025
The HIPAA Journal previously reported on another affected client, Hamilton County in Tennessee. The post Medical Express Ambulance Service Data Breach Affects 118K Individuals appeared first on The HIPAA Journal. Rhea Medical Centers investigation is ongoing, but it has been confirmed that up to 8,309 individuals have been affected.

The HIPAA Journal
APRIL 1, 2025
The post 173,000 Patients Affected by Chord Specialty Dental Partners Email Data Breach appeared first on The HIPAA Journal. Chord Specialty Dental Partners said its policies and procedures related to data security have been reviewed and will be enhanced, as appropriate, to prevent similar incidents in the future.

Arkenea
MARCH 29, 2025
Having a profound understanding of the HIPAA rules puts you one step ahead in the healthcare sector. HIPAA risk assessment ensures that ePHI is protected from threats and vulnerabilities such as fraud, data breaches, financial scams, identity thefts, etc. HIPAA Compliance Checklist 1.

Sensible Medicine
MARCH 25, 2025
For example, the Feinstein Institute for Medical Research settled HIPAA violations for $3.9 Sharing data that includes sensitive patient health information, exposes researchers and institutions to significant legal and financial risks. million after being accused of mishandling a laptop containing protected health information.

The HIPAA Journal
MARCH 19, 2025
The post Cyberattack on Michigan Plastic Surgery Practice Affects Almost 20,000 Patients appeared first on The HIPAA Journal.

The HIPAA Journal
MARCH 28, 2025
The post Beacon Health System Affected by Two Business Associate Email Breaches appeared first on The HIPAA Journal. Neither incident is currently shown on the HHS Office for Civil Rights breach portal, so it is unclear how many patients have been affected.

Arkenea
MARCH 31, 2025
HIPAA compliance costs can greatly vary depending on the kind of application you’re developing. Developing a healthcare application that complies with the Health Insurance Portability and Accountability Act (HIPAA) is essential for safeguarding sensitive patient information and adhering to legal standards.

Open Dental
AUGUST 6, 2024
We debunk some common IT myths and offer practical tips to help dental offices maintain robust cybersecurity and ensure HIPAA compliance. The post IT Myths and Misconceptions in Cybersecurity and HIPAA Compliance for Dental Offices appeared first on Open Dental Blog.

99MGMT
JUNE 14, 2024
Social media has become an integrated part of today's world, and it is no surprise that it plays an increasingly important role in our lives. As healthcare professionals, you know the importance of staying up-to-date with the latest technologies, including social media-related ones.

Arkenea
APRIL 8, 2025
Key Takeaways Healthcare developers must follow the three key HIPAA rules during API development: HIPAA security rule, privacy rule, and the breach notification rule. Further, HIPAA compliant healthcare APIs protect the security and privacy of ePHI during data exchange. Key Rules for Developing a HIPAA API 1.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content